One of the most powerful uses for digital credentials is the exchange of data between departments or even entirely separate organizations.
A job candidate should be able to prove education and employment. A customer should be able to prove membership in a loyalty program and the receipt of past transactions. A patient should be able to prove insurance and health history. But the individual’s data currently sits in each organization’s centralized database or “silo.”
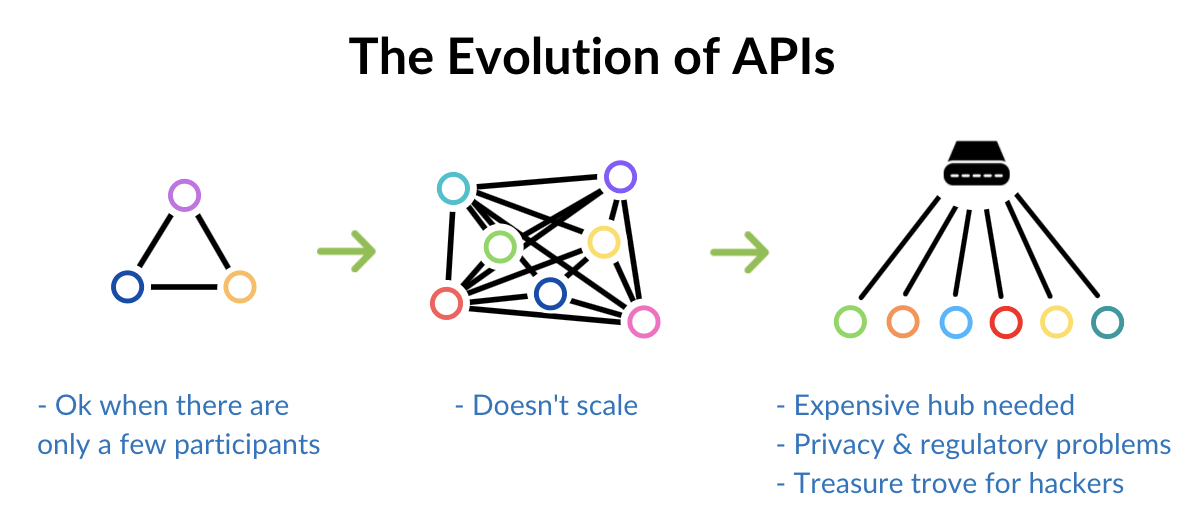
Historically it has been necessary to set up complex and costly technical integrations between each data silo. Network effects mean that such integrations can never scale. The more participants are involved, the greater the complexity as connections multiply and costs rise exponentially.
As a consequence, the temptation is to put a big database in the middle that everyone connects to. That has obvious drawbacks: it creates a hacking treasure trove, can break numerous privacy regulations, and costs a lot of money to set up and maintain.
If you look at each of these data silos, you’ll see a common denominator: The individual the data pertains to.
So then…
If the individual is at the center of this data, why can’t we have the individual control and move the data around for us?
An excellent example of this multi-silo situation is the airline industry and the ecosystem they need to carry out pre-departure tests. The below diagram from IAG (parent company of British Airways) gives you an idea of what is involved in checking if a passenger is OK to depart, in light of destination-specific requirements like travel insurance, proof of accommodation, and vaccine records..
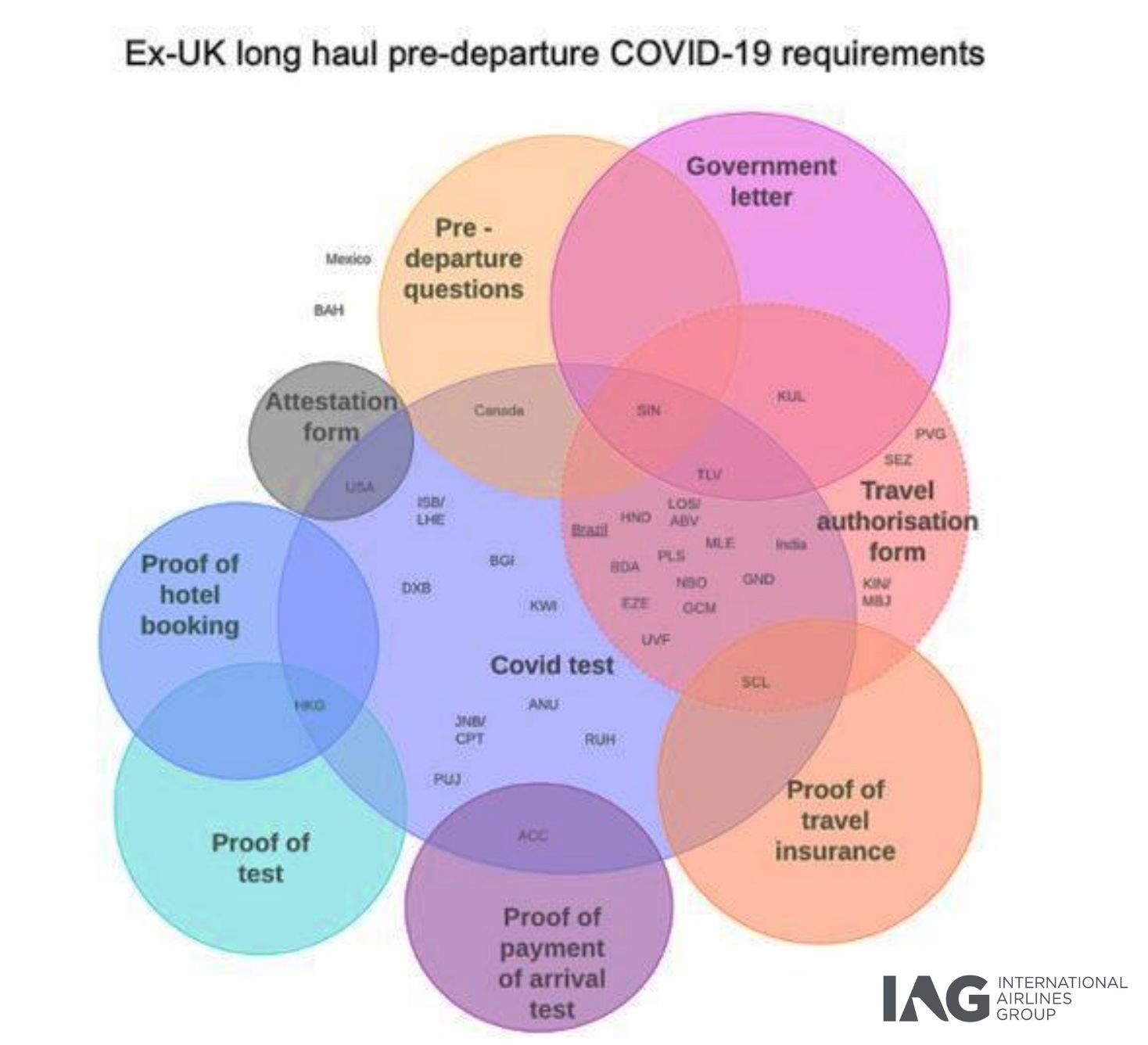
And this is just one airline group. Imagine this diagram replicated for every airline, and then multiply that by the number of airports, and multiply that by the number of test labs. It quickly becomes untenable to try and knit these silos together, and nobody wants a huge global database containing everyone’s health status.
A better way is so simple it’s amazing it hasn’t been done before. Why not give the data to the customer or employee or user, and they can carry it with them and present it at the right place at the right time?

Why hasn’t this been done before?
Of course, it has, with physical paper and plastic credentials. Give an employee an ID badge and they will carry it with them and show it whenever they need to get into a building. Give a passenger a passport and they can show it at check in, at the gate, on the plane, and on arrival. We’ve been doing this with physical credentials for a long time.
Until recently it hasn’t been possible to do this digitally in a way that preserves the privacy of the individual and the authenticity of the data. Now it is.
Advances in decentralized identifiers (DIDs) and verifiable credentials (VCs) mean that it is now possible to give someone some data, and they can carry it and present all of it or just portions of it to a third-party, who can instantly verify its source and integrity. Without needing any central intermediary or hub. And without the third-party needing to connect to any of the data issuers.
It is no accident that the International Air Transport Association (IATA) is using exactly this technology for their IATA Travel Pass solution. Providing the airline passenger with digital versions of their passport and COVID-19 test status means the passenger can use that data anywhere they want, under their control, and IATA doesn’t need to set up a complex and expensive central hub to hold and verify everything.
This way, hundreds of airlines, labs, and airports around the world can interoperate without ever having to connect with each other. It is highly efficient and cost effective.
The same digital credential technology can be used for any data and could in the near future include vaccination status, boarding passes, meal preferences, car rental booking confirmation, etc. And a passenger can provide this data ahead of time and be pre-checked, resulting in totally contactless departure and arrival.
Let’s look at another example of a multinational financial services company with many business units and departments. Each department simply gives the customer a digitally verifiable credential confirming their relationship. The mortgage team gives the customer a credential detailing their mortgage. The insurance team gives the customer a credential detailing their insurance policy. It’s all rather like sending the customer pieces of paper, but digital, standardized, and cryptographically verifiable. Just like in their paper filing cabinet, the customer now has a digital record, that they control, of all their relationships with this global company.
When the customer then applies for a new product like a car loan from the same company, the company simply asks the customer “to speed up your application, please confirm the details of other products you have from us.” The customer’s phone goes “ping” and they see the request, already filled in with data from the credentials they already have. The customer sends this “proof” directly and securely to the car loan department, which can verify the source and authenticity of the data instantly.
The customer becomes the integration point. The customer is the API. Rather than having one huge, expensive, and probably illegal data hub, every customer becomes a data hub in their own right. They provide the data needed, just-in-time, under their control.
There are even more advantages of this approach:
- The customer now has a valuable set of digital credentials that they can use anywhere else, to prove things like their address, age, that they have a bank account and so on to anyone, anywhere.
- You can eliminate usernames and passwords, as the customer can use the credentials an organization gave them to identify themselves when they call in, walk in, or log in.
- You can send secure 1–1 messages and exchange other data using the same technology. As the customer and the organization can securely identify each other, and they have a private communication channel between each other, new types of relationship become possible.
The result is that you go from enormous multi-million dollar integration and CRM projects, to small, fast, departmental implementations of simple credential issuing and verifying platforms.
Organizations can use the same open-source technology to handle two-factor authentication, new customer onboarding, returning customer authentication, new product sales, consent management, and secure customer communications.
This is a strategic solution, not a tactical one.
Ready to make the change to a better, more scalable way of handling data? Register a Developer Account with Evernym to gain free access to the tools, resources, and support needed to integrate verifiable credential technology into your organization’s workflows.