Today’s digital identity is idiotic.
Compared to physical paper documents or credentials, our digital identities are forgettable, restrictive, and borderline useless. For all intents and purposes, when we go online “we the people” become meaningless identifiers, assigned for someone else’s convenience.
With today’s digital identity, your data is locked in some organisation’s silo. All you have is a username and password, which is useless anywhere else.
By contrast, your paper passport can be used in hundreds or thousands of ways anywhere in the world. To prove your age, your name, your nationality, or where you have travelled. You carry it with you, and you can show it privately to anyone you want at any time, without the passport office knowing or caring.
Imagine if the passport office kept your passport in a safe with all the other millions of passports. When you wanted to travel somewhere you had to call them, give a unique username and password that you’ve probably forgotten, and hand over the phone to the border patrol agent to confirm that you can travel. Nobody would ever tolerate that. Airports and train stations would grind to a halt. Worse still, imagine if you had to call your travel agent, who then called the passport office for you, and while doing so they copied all your passport details and sold them to the highest bidder.
Unacceptable, right?
Yet that is how things work in the digital world.
With today’s digital identity, your data is locked in some organisation’s silo
Now replicate this scenario across all your relationships and all your credentials, and it’s no wonder things are so broken online.
The obvious answer is to give people credentials that they can carry with them. We figured this out in 450 BC when the first “safe travel” letter was issued to Nehemiah by King Artaxerxes of Persia. Note that this safe travel letter was not an “identity”. It was a credential that could be used to prove something about the holder in a specific context , in this case, that the holder was granted safe passage through foreign territory. This is an important distinction.
More recently, the term “self-sovereign identity” has been coined to categorise digital identity that is secure, controllable, and portable. In my 2016 paper titled “The Inevitable Rise of Self-Sovereign Identity”, I took Christopher Allen’s Ten Principles of Self-Sovereign Identity and summarised them into three sections for simplicity:
| Security
the identity information must be kept secure |
Controllability
the user must be in control of who can see and access their data |
Portability
the user must be able to use their identity data wherever they want and not be tied to a single provider |
| Protection | Existence | Interoperability |
| Persistence | Control | Transparency |
| Minimisation | Consent | Access |
| Portability |
Amazingly, all of these are also characteristics of paper documents (though the security side of paper can be radically improved with the latest cryptographic techniques). Paper is, in fact, the most widely used global standard for credentials in existence today.
It is fairly simple to conclude that self-sovereign identity is not a new thing at all. Nehemiah’s “passport” was portable, controlled by him, and likely bore the King’s seal giving it an element of security. We just never called it “self-sovereign identity”.
It is fairly simple to conclude that self-sovereign identity is not a new thing at all.
Yet, this age-old concept faded with the advent of the Internet. Suddenly, an individual’s identity morphed into thousands of different online identities as users were asked to register a separate account for every website they used. And it became clear that the Internet was designed to connect devices, not users.
There was no standard way of issuing, holding, and verifying digital credentials, leaving in their place a slew of workarounds that opened doors to fraud, exploitation, data theft, and complexity at a scale never before imagined.
I call this “The Chasm of Chaos”.
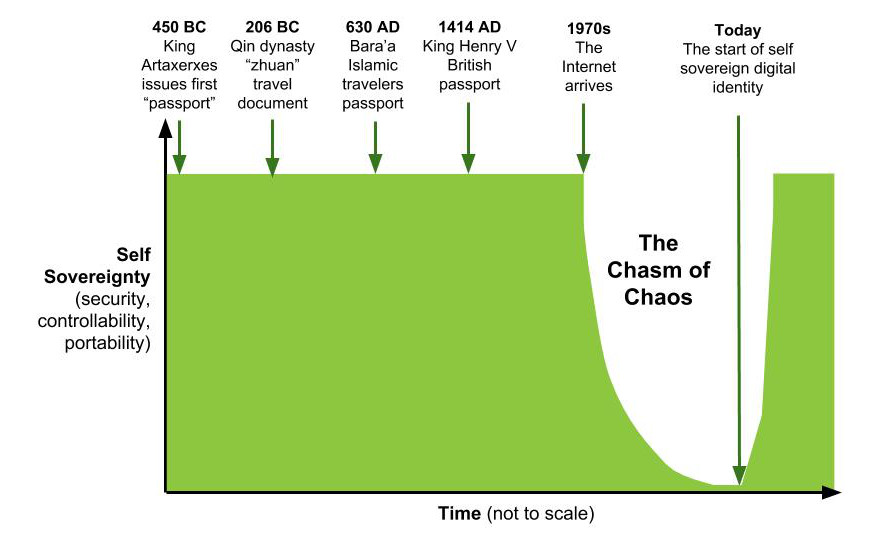
In fact, everything you know about digital identity is a work-around, developed while we figure out how to do things properly and enable everyone to issue, hold, and verify digital credentials.
It became clear that the Internet was designed to connect devices, not users
In the Art of War, Sun-Tzu said “in the middle of chaos, there is also opportunity”. This couldn’t be more appropriate. Into the Chasm of Chaos have stepped new global businesses that exploit these work-arounds to create vast data engines, promoting wholesale private data exploitation as convenience and simplicity, thus prolonging the pain.
What has been stopping us? Why have we been stuck with the Chasm of Chaos for so long?
Before I answer that, it’s important to briefly clarify a few pieces of terminology. There’s a lot of confusion in the industry that doesn’t help the lay person (and many self-proclaimed experts) to understand the situation. We tend to confuse through injudicious creation of complex terminology. In reality, there’s nothing new here: It’s just like what we do every day with physical credentials, but with some new cryptographic superpowers.
- Self-sovereign does not mean “self-attested”. To be self-sovereign, you manage and control your credentials and relationships without needing a 3rd party. Anyone can issue credentials to you, including yourself (and if so, it would be those credentials that would be “self-attested”).
- A credential is like a passport or university degree certificate or pilot’s license. The data within are “attributes” (e.g., name, date of birth). You already acquire many credentials during your life. A digital credential is simply a set of digitised attributes wrapped together with some clever cryptography.
- Using the correct cryptographic techniques, it is possible to mix and match attributes from different credentials (e.g., two proofs of address and proof of citizenship) and even answer “yes/no” to a challenge like “are you over 18” without revealing the underlying attribute itself. These are called zero-knowledge proofs).
- You don’t have “one identity”. You have a set of credentials. You can use them in many different ways (often called “personas”). It’s just like the paper and plastic credentials you have now.
- When you’re asked to prove something about yourself, the requestor may ask for data from a specific type of issuer (e.g., a recognised passport authority). You can elect whether to share this or not in order to achieve something. The requestor decides whether or not to trust the credential issuer.
- Your “identity” is therefore specific to a certain context. You can be an employee of a company, while simultaneously being an international traveller, a father of two children, and a member of a sports club. In each context, you will have shared attributes from different credentials.
To make this work and deliver a way out of the Chasm of Chaos, two things are required:
- An open, common protocol for issuing, holding, and verifying digital credentials. Something a bit like SMTP is for email, that is non-proprietary. and which anyone can build on and use. This is the purpose of the Sovrin Protocol, as delivered in the open source Hyperledger Indy codebase invented by Evernym.
- Somewhere to store the public key and other information necessary to cryptographically verify the issuer of a digital credential so that anyone can confirm the authenticity of an attribute, without having to contact the issuer (and thus, ruin the privacy of the credential holder). Importantly, this store needs to be extremely tamper-resistant, chronologically sequenced, and not owned by any single party. This is the purpose of the Sovrin ledger, a global, decentralised instantiation of the Hyperledger Indy codebase.
Assuming these two things exist, people, organisations, and things will be able to issue, hold, and verify digital credentials in a way that is private and secure. Most importantly, any verifier will be able to carry out four checks on any attributes that they receive, without having to contact the issuer. I call this the “quad-lock”:
The Quad-LockThe four checks any verifier can do, simply by reading the Sovrin Network |
|
| Who issued the credentials? | Were they issued only to the holder who is presenting them? |
| Have the attributes in the credential been tampered with? | Has the issuer revoked the credential? |
Once anyone can carry out these four checks, anywhere in the world, at any time, without having to have APIs or integrations to every possible issuer in the world, you finally achieve Internet-scale verification, with built-in privacy and security.
At the time of writing, over 60 organisations on six continents have already volunteered to run a node of the Sovrin ledger since Evernym launched it and gave it away in September 2016. And this number is increasing every month. With the infrastructure in place and becoming more robust every day, it is now possible to see a way out of the mess we’ve created. To enable us to return to a self-sovereign world.
The world of digital self-sovereign identity will be even better, more secure, and more private than the paper one. With credential digitisation comes convenience and cryptographic superpowers that have not been possible before, such as:
- The ability to backup and recover credentials, which is simply not possible with paper.
- Proving our identity securely over a distance without needing to rely on intermediaries.
- Sharing simple yes/no answers which are verifiable as authentic, without sharing the underlying data.
- Having a unique, private and secure connection with each of our relationships that nobody can snoop on.
- Allowing verifiers to check credential authenticity and validity without ever having to contact the credential issuer and without harming the privacy of the credential holder.
- Enabling credential issuers to revoke credentials once issued, with no need to open up complex APIs and integrations to their systems.
- Using the same protocol for people, organisations, and things.
Self-sovereign identity is happening. Again.
Now that the technology is available, the return to self-sovereignty is inevitable.
There will be wholesale and dramatic improvements to the online user experience. No longer will we need to repeatedly fill in forms, manage hundreds of usernames and passwords, struggle with typing in credit card data, or do that Captcha thing. Finally online businesses will be able to rely on the data they get from people, organisations, and things. Friction will fall away. Signup for anything will take a couple of seconds. Organisations won’t need to hoard vast amounts of customer data any more as it will be so simple to just ask for it again to execute a transaction. Silos within and across organisations will disappear as people become the couriers for data between them. Phishing will plummet as you will know that a communication comes from your bank or insurer because you have a unique, secure, and persistent connection with them, and you can ask them to prove who they are in seconds.
The workarounds that have been put in place in the digital world that cause so much friction and result in so much bad behaviour will no longer be needed.
The era of assigning meaningless identifiers to people is over.
Now that the technology is available, the return to self-sovereignty is inevitable. There will be powerful forces trying to prevent it for obvious reasons—it will “move the cheese” of companies who have built a business on the inefficiencies, insecurities, or other vulnerabilities of the Chasm of Chaos. But these forces will soon be overcome by the realization that the return to self-sovereign identity is so dramatically better. That open is better than closed. That giving people digital credentials is better than keeping them locked in corporate databases. That the combination of convenience, security, and privacy delivers game-changing improvements in user experience.
People will love the results – no need to remember hundreds of usernames and passwords, no more hounding by inaccurate advertising and spam, and finally getting more security AND more convenience. Those that want to remain in their closed ecosystems will be out-competed and out-maneuvered by this fundamental shift.
It’s happening now. The era of assigning meaningless identifiers to people is over. It’s time to power-up our digital credentials.
Thanks for reading!Want more resources on all things self-sovereign identity? |