What Are Verifiable Credentials?
The tangible credentials we all use—driver’s licenses, passports, birth certificates, car titles, and plane tickets, for example—are now being re-imagined as digital files. We can carry these digital credentials on smartphones, index and search them, back them up, and make perfect copies of them on demand.
But while digital records are nothing new, today’s credentials come with certain ‘cryptographic superpowers’ that make them tamperproof, secure, and verifiable. Whereas a simple digital copy of a car title can easily be edited, a digital verifiable credential is one that has been issued by a trusted authority for, and only for, its holder.
With these superpowers comes an array of benefits for businesses, governments, and individuals alike. For consumers, they make it easier to interact with the digital world, offering a sort of universally trusted digital passport for verifying our identities online. For governments, they unlock opportunities for new economic growth through creating an underlying framework of trust between businesses and consumers. And for businesses, they can be used to automate workflows that are cumbersome today, improve trust and accountability, improve security, reduce fraud, and drive administrative efficiencies.
These advantages are compelling, and they make digital credentials an obvious component of a multidimensional, self-sovereign identity.
How Verifiable Credentials Work
When digital credentials conform to the W3C’s Verifiable Credentials Data Model, they are called verifiable credentials (VCs). They facilitate interactions using a pattern called the triangle of trust:
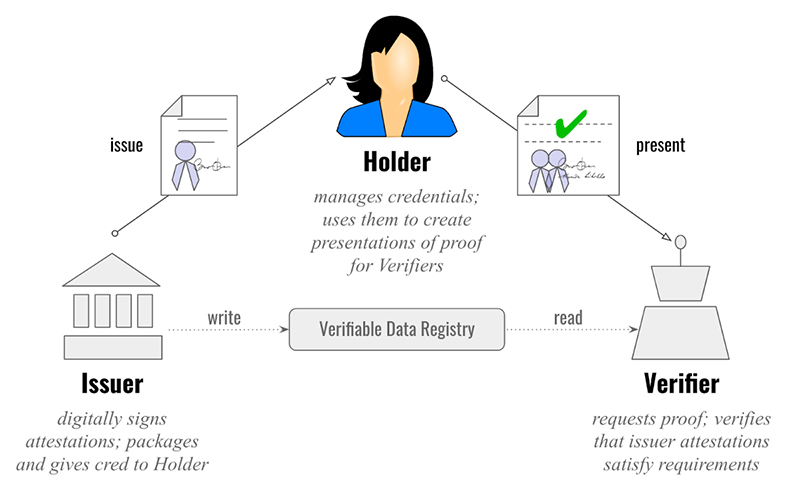
Issuers create credentials, holders store them, and verifiers ask for proof based upon them. Verifiable presentations are packages of evidence—either credentials, or data derived from one or more credentials—built by holders to satisfy a verifier’s requirements. Verifiers learn with certainty which issuers have attested something by checking digital signatures against a verifiable data registry (typically, a blockchain).
So what does all of this mean? Well, it upgrades how we manage digital identity today:
- No more tedious back-and-forth between verifiers and issuers. With verifiable claims, the verifier no longer has to contact the issuer to confirm the credential. This can save admin-heavy industries like healthcare and insurance hundreds of billions each year in data verification costs. (Note: Verifiers still reserve the right to determine if an issuer is trustworthy or not.)
- The holder keeps control and ownership over her identity. Holders choose what they want to disclose, and to whom they want to disclose it. They can share only the required information, and nothing more. For example, they can prove they are a registered voter who hasn’t yet cast a ballot, without revealing their name or government ID number.
This all provides decentralization, flexibility, and freedom.
(Note: Icons at each corner of the triangle are arbitrary; institutions, individuals, and IoT things can each play any role in the triangle of trust.)
Vital Issues With Verifiable Credentials
Not all approaches to digital credentials are equally safe or powerful. Digital credentials must address important concerns before they achieve their promise:
- They need a standard, open format, so software that handles them can interoperate.
- They need a secure, vetted verification process, so they can’t be shared or used to commit fraud.
- They need a robust privacy strategy, so they can comply with regulatory requirements across legal jurisdictions, and so they avoid abuse in the surveillance economy.
The W3C standard for verifiable credentials begins to address these issues. Verifiable credentials are structured in an interoperable way. The attestations that they make are backed by another standards-track technology, Decentralized Identifiers (DIDs). They use industrial-strength, peer-reviewed cryptography, and the digital signatures that endorse them have documented algorithms for verification. A test suite and reference implementations in open source provide additional confidence.
Other approaches to digital credentials do exist. The airline industry has a standard for bar-coded boarding passes; ISO is working on global conventions for driver’s licenses; various technologies publish digitally signed documents to or with blockchains. However, only the W3C verifiable credentials spec combines the gravitas of a global standards organization, a scope that includes all types of credentials, and full compatibility with recent innovations in blockchain-oriented, decentralized identity. Thus, momentum on verifiable credentials is strong. Deployments are underway around the world for financial services, healthcare, travel, IoT, government, education, and refugee and vulnerable population use cases.
More Information
Verifiable credentials are a young technology. Those of us who work on the spec and its implementations as a full-time job know that the W3C standard is just a beginning—not a last word—on the important issues identified above. It specifies a data model, but not the actual format of digital files. Because it permits divergence on some pivotal questions, interoperability is not as good as it should be, yet. Verification processes need to go beyond digital signatures to complex criteria. Rich schemas for credentials need elaboration. A full threat model for credentials is under discussion, and different approaches to privacy are competing for mindshare.
In coming posts, I’ll explore these issues in greater depth. I hope you’ll end up with a clear idea how to navigate the complex, rapidly changing landscape of verifiable credentials, harvesting their goodness for yourself.
More in this series:
- Categorizing Verifiable Credentials: An exploration of the different types of credentials that exist today and the architectural choices driving these differences
- The Dangerous Half-Truth of “We’ll Be Correlated Anyway”: An argument for choosing non-correlating credentials over correlating credentials despite the oft-cited belief that some level of identity correlation is inevitable in today’s surveillance economy
- Evernym Webinar: Verifiable Credentials What we can learn from how credentials are managed in the physical world